Code scanning is a feature of GitHub Advanced Security that you use to analyze the code in a GitHub repository to find security vulnerabilities in your software. Any problems identified by the analysis are shown in GitHub.
For this demo we'll make use of the WebGoat, a deliberate insecure web application maintained by OWASP designed to teach web application security lessons.
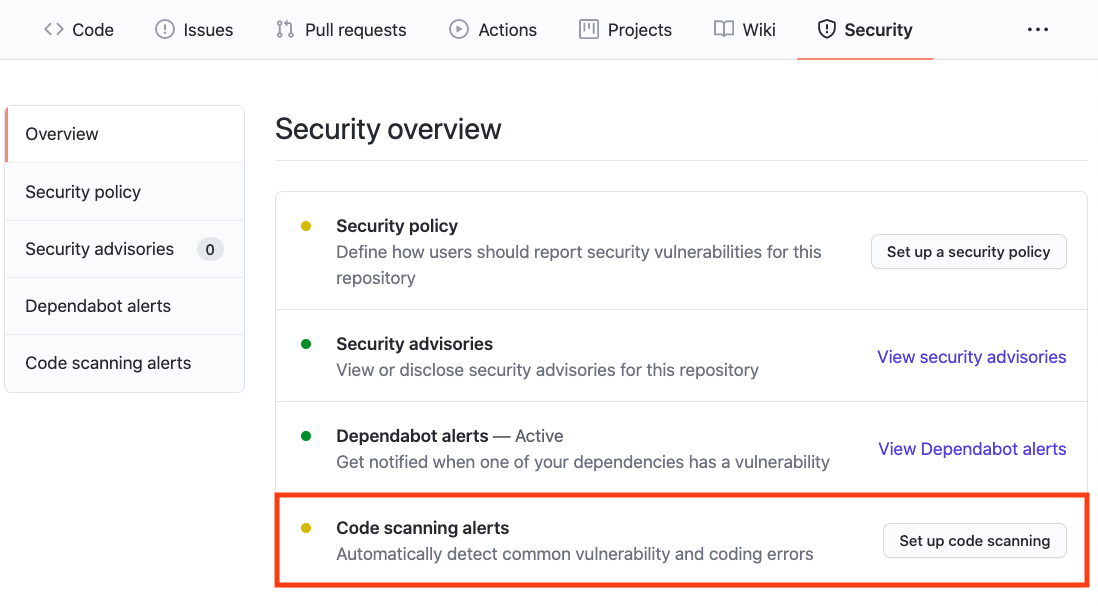
Enable Code Scanning
Click on the Security tab.

Click the Setup this workflow button by CodeQL Analysis.
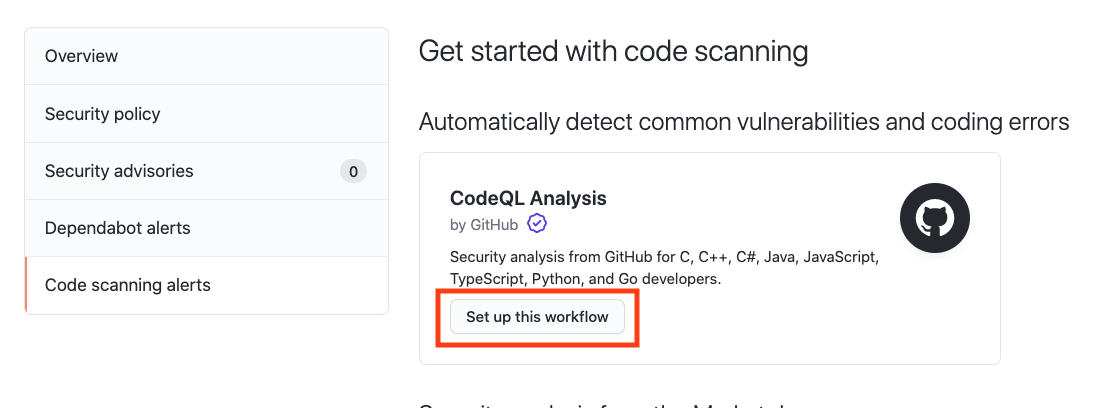
This will create a GitHub Actions Workflow file with CodeQL already set up. Since Javascript is an interpreted language there is no need to configure any builds. See the documentation if you would like to configure CodeQL Analysis with a 3rd party CI system instead of using GitHub Actions.
Actions Workflow file
The Actions Workflow file contains a number of different sections including:
- Checking out the repository
- Initializing the CodeQL Action
- Running a build (or use autobuilder)
- Running the CodeQL Analysis
For this demo we'll manually run the build steps of this application. Comment out the autobuild step and copy paste the following snippet to build this application:
- name: Set up JDK 15
uses: actions/setup-java@v2
with:
distribution: 'zulu'
java-version: 15
architecture: x64
- name: Build with Maven
run: mvn clean install
Click Start Commit -> Commit this file to commit the changes to develop branch.
Workflow triggers
There are a number of events that can trigger a GitHub Actions workflow. In this example, the workflow will be triggered on

- push to main branch
- pull request to merge to main branch
- on schedule, at 6:33 every Thursday
Setting up the new CodeQL workflow and committing it to main branch in the step above will trigger the scan.
GitHub Actions Progress
Click Actions tab -> CodeQL
Click the specific workflow run. You can view the progress of the Workflow run until the analysis completes.

Security Issues
Once the Workflow has completed (this will take about 5 minutes), click the Security tab -> Code Scanning Alerts. An security alert "Resolving XML external entity in user-controlled data)" should be visible.
Clicking on the security alert will provide details about the security alert including: A description of the issue A tag to the CWE that it is connected to as well as the type of alert (Error, Warning, Note) The line of code that triggered the security alert The ability to dismiss the alert depending on certain conditions (false positive? won't fix? used in tests?)

Click Show more to view a full desciption of the alert including examples and links to additional information.


Show Paths
CodeQL Analysis is able to trace the dataflow path from source to sink and gives you the ability to view the path traversal within the alert.
Click show paths in order to see the dataflow path that resulted in this alert.


Fix the Security Alert
In order to fix this specific alert, we will need to ensure disable the parsing of this user-controlled data.
Click on the Code tab and Edit the webgoat-lessons/xxe/src/main/java/org/owasp/webgoat/xxe/Comments.java file. Navigate to Line 97 of the `Comments.java file and modify the line:
var xsr = xif.createXMLStreamReader(new StringReader(xml));to
xif.setProperty(XMLInputFactory.SUPPORT_DTD, false);
xif.setProperty("javax.xml.stream.isSupportingExternalEntities", false);
var xsr = xif.createXMLStreamReader(new StringReader(xml));Click Create a new branch for this commit and start a pull request, name the branch fix-xml-reader, and create the Pull Request.
In the Pull Request, you will notice that the CodeQL Analysis has started as a status check. Wait until it completes.

After the Workflow has completed click on Details by the Code Scanning Results / CodeQL status check.

Notice that Code Scanning has detected that this Pull Request will fix the vulnerability that was detected before.

Merge the Pull Request. After the Pull Request has been merged, another Workflow will kick off to scan the repository for any vulnerabilties.
After the final Workflow has completed, navigate back to the Security tab and click Closed. Notice that the XML external identity alert now shows up as a closed issue.

Click on the security alert and notice that it details when the fix was made, by whom, and the specific commit. This provides full traceability to detail when and how a security alert was fixed and exactly what was changed to remediate the issue.

Ready to talk about advanced security features for GitHub Enterprise? Contact Sales for more information!
Check out GitHub's Security feature page for more security features embedded into GitHub.
Check out the Code Scanning documentation for additional configuration options and technical details.
