Welcome to the code scanning for Terraform demo! For this demo we'll make use of "TerraGoat", a "Vulnerable by Design" Terraform repository created by Bridgecrew. TerraGoat is a learning and training project that demonstrates how common configuration errors can find their way into production cloud environments, and how you can use GitHub Advanced Security with tfsec to find these vulnerabilities.
Code scanning is a feature of GitHub Advnaced Security that you use to analyze the code in a GitHub repository to find security vulnerabilities in your software. Any problems identified by the analysis are shown in GitHub.
Code scanning allows you to fully integrate your favorite (open source) scanning tools so all relevant information is shown to the developer the moment a vulnerablity is identified.
This demo shows you how you can integrate tfsec and/or bridgecrew to scan your terraform definitions for vulnerablities.
Enable Code Scanning
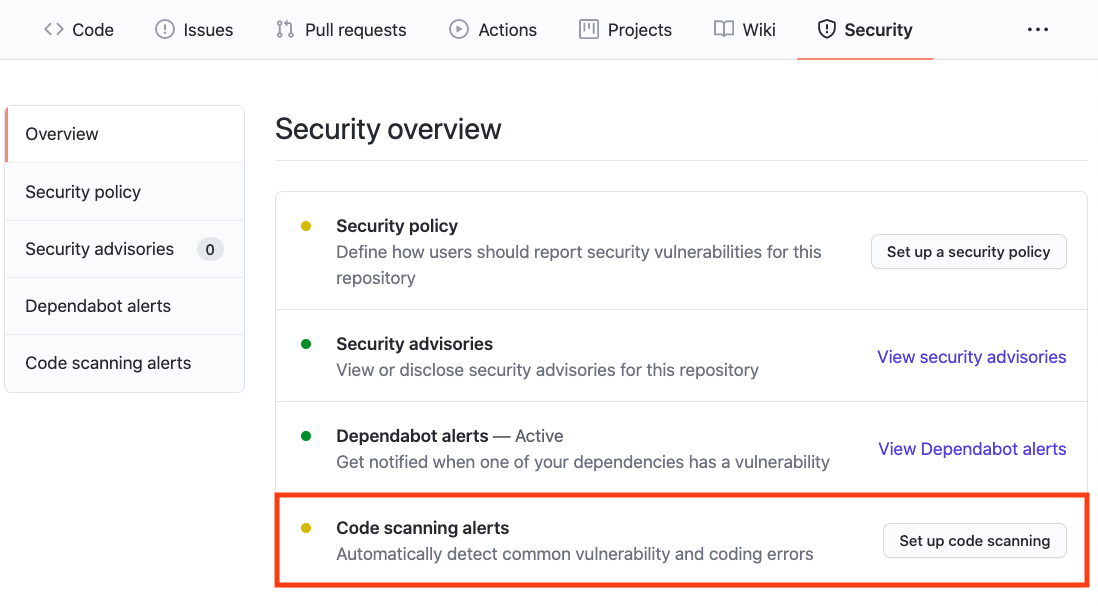
Click on the Security tab.

Click Set up code scanning.
Click the Setup this workflow button by tfsec.

GitHub Code Scanning analyses which programming languages are used in a repository, and provides suggestions for scanning tools based on this information. Other scanning tools that are available in the overview include Bridgecrew, Kubesec, and others.
See tfsec's documentation for more information about configuring this tool.
Actions Workflow file
The Actions Workflow file contains a number of different sections including:
- Checking out the repository
- Run tfsec
- Upload results

Click Start Commit -> Commit this file to commit the changes to main branch.
Workflow triggers
There are a number of events that can trigger a GitHub Actions workflow. In this example, the workflow will be triggered on

- push to main branch
- pull request to merge to main branch
- on schedule, at 05:21 UTC on Thursdays.
Setting up the new actions workflow and committing it to main branch in the step above will trigger the scan.
GitHub Actions Progress
Click Actions tab -> tfsec
Click the specific workflow run. You can view the progress of the Workflow run until the analysis completes.

Security Issues
Once the Workflow has completed, click the Security tab -> Code Scanning Alerts. An security alert "EKS cluster should not have open CIDR range for public access" should be visible.
Clicking on the security alert will provide details about the security alert including:
- A description of the issue
- The line of code that triggered the security alert
- A tag to the type of alert (Error, Warning, Note)
- The ability to dismiss the alert depending on certain conditions (false positive? won't fix? used in tests?)
- A link to tfsec's documentation for more information about the rule and mitigations options

Fix the Security Alert
In order to fix this specific alert, we will need to that we our CIDR range doesn't have public access.
Click on the Code tab and Edit the terraform/aws/eks.tf file. Navigate to Line 68 of the eks.tf file and modify the line:
vpc_config {
endpoint_private_access = true
subnet_ids = ["${aws_subnet.eks_subnet1.id}", "${aws_subnet.eks_subnet2.id}"]
}to
vpc_config {
endpoint_public_access = false
public_access_cidrs = ["10.2.0.0/8"]
subnet_ids = ["${aws_subnet.eks_subnet1.id}", "${aws_subnet.eks_subnet2.id}"]
}Click Create a new branch for this commit and start a pull request, name the branch eks-endpoint-fix, and create the Pull Request.
In the Pull Request, you will notice that the tfsec Analysis has started as a status check. Wait until it completes.

After the workflow completes, click on Details by the Code scanning results / tfsec status check.

Notice that Code Scanning has detected that this Pull Request will fix two vulnerabilies that were detected before.

Merge the Pull Request. After the Pull Request has been merged, another Workflow will kick off to scan the repository for any vulnerabilties.
After the final Workflow has completed, navigate back to the Security tab and click Closed. Notice that the two alerts now shows up as closed issues.

Click on the security alert and notice that it details when the fix was made, by whom, and the specific commit. This provides full traceability to detail when and how a security alert was fixed and exactly what was changed to remediate the issue.

Ready to talk about GitHub Advanced Security and Code Scanning? Contact Sales for more information!
Check out GitHub Advanced Security for more information about GitHub Advanced Security.
Check out our documentation for more information and configuration options.
