-
Notifications
You must be signed in to change notification settings - Fork 435
1. FAQ
PE-sieve is a light-weight tool that helps to detect malware running on the system, as well as to collect the potentially malicious material for further analysis.
Recognizes and dumps variety of implants within the scanned process, such as:
- replaced/injected PEs
- shellcodes
- hooks, and other in-memory patches.
Detects inline hooks, Process Hollowing, Process Doppelgänging, Reflective DLL Injection, etc.
It can be used for dynamic malware unpacking (see examples here).
PE-sieve works on Windows, the lowest supported version is XP.
📦 ⚙️ You can download the latest stable version from releases. You can also find it i.e. at Chocolatey.
🧪 Fresh test builds (ahead of the official release) can be downloaded from the AppVeyor build server. They are created on each commit to the master branch. You can download them by clicking on the build version, then choosing the tab Artifacts. WARNING: those builds may be unstable.
🚧 If you want to build it by yourself from the sources, follow this small guide.
This tool is intended to help malware analysts, malware hunters, and incident responders in their daily work.
Having a new sample to be analyzed, we can unpack it with PE-sieve very fast, extracting the payload that can be then easily identified and used for further analysis.
When we want to collect material from an infected system of a client, HollowsHunter (an extended PE-sieve based scanner) can scan the full system, dumping the injected code from each and every accessible process.
It can also help in cases when the infected client doesn't know what is the sample that started the infection. PE-sieve/HollowsHunter will search for injected material in running processes, and then dump the malicious PE.
Not really. PE-sieve hints about suspicious indicators, however it does not give a final judgment if the process was in fact malicious. For example, it detects hooks - but it cannot judge if the hook was done for malicious or for legitimate purpose. So, its role is rather to supply a raw material for further processing/analysis, and to hint what are the processes you should examine closer.
I need to emphasize it again: PE-sieve is a tool to detect code implants, not to make a judgment about them. It will detect all sort of hooks, hot-patching, and modifications in a process. There are multiple reasons why such modifications can be installed, and they may not necessarily be malicious.
You can expect JIT (Just-In-Time compiled code) in .NET applications. It will result in detecting shellcodes and some patched modules (i.e. clr.dll).
You can expect hooked modules in some browsers, i.e. Firefox. In order to distinguish which hook is harmless, look where it leads to. Example of a harmless hook (leads to mozglue.dll, which is a legitimate target):
17be0;BaseThreadInitThunk->5a622e30[5a620000+2e30:mozglue.dll:0];5
PE-sieve may be especially noisy in a presence of some antivirus software - just because they do monitor applications by hooking them. Lots of AV products actually use similar techniques as malware do. Detecting modifications done by legitimate software is not a bug, but an intended functionality, helping to gather details on what are the hooks installed at what locations. PE-sieve also detects shims, and other in-memory patches which may be malicious in some cases, but also may be used to apply fixes in application.
Once you made sure that the patches in particular modules are legitimate, you can exclude those modules from the scan using /mignore option.
In the future I am planning to implement whitelists, so that users will be able to regulate the level of details that they want to see, and reduce the noise.
See the following slides for the detailed explanation
In order to perform a basic scan, you just need to supply the PID of the target process:
pe-sieve.exe /pid <target_pid>
For example, if I suspect that the process svchost.exe is infected, and I want to scan it:
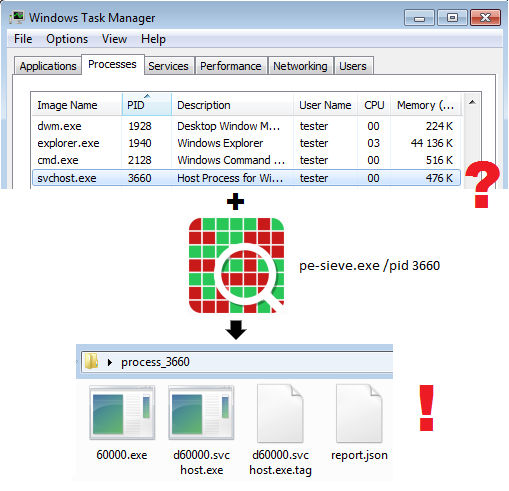
If the process was indeed infected, malware has injected its implants inside. PE-sieve will detect them and dump into a dedicated folder, along with JSON reports describing details of the detected material. The implanted PE files will be automatically unmapped, reconstructed, and ready to be analyzed by other tools. If any of the modules within the process was hooked or patched, PE-sieve will generate a TAG file, helpful in investigating the changes.
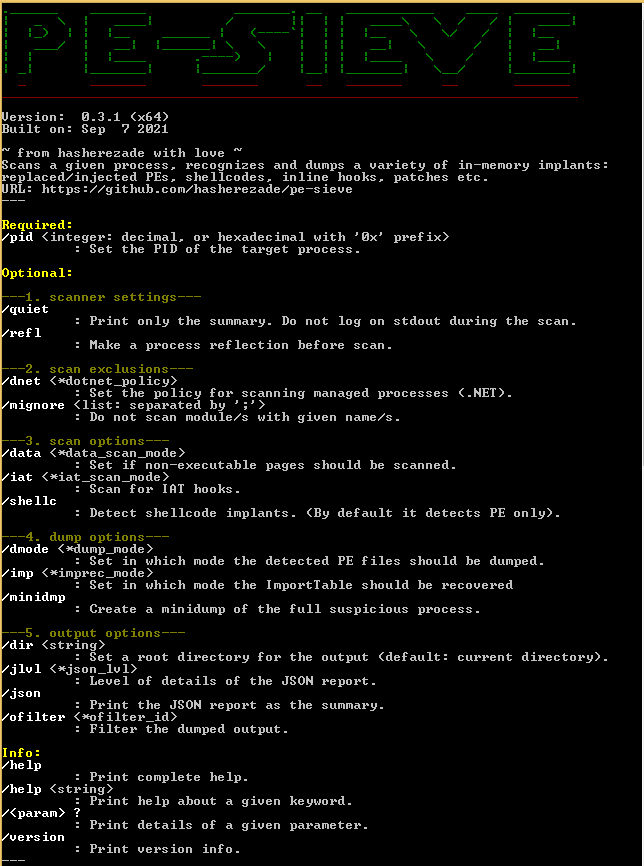
PE-sieve comes with a simple command-line interface. The parameters allows to extend the functionality beyond the default scan. To see the full list of commands, you can deploy it without any parameters.
PE-sieve is meant to be a light-weight engine dedicated to scan a single process. It can be built as an EXE or as a DLL. The DLL version exposes a simple API and can be easily integrated with other applications.
There are few other tools that use PE-sieve as an engine, but focus on some specific use-cases. They offer additional features and filters on the top of its base.
- HollowsHunter - allows to scan multiple processes, the targets can be selected by various criteria
- MalUnpack - offers quick unpacking of a supplied malware sample
If instead of scanning a particular process you want to scan multiple processes, or even your full system with PE-sieve, you can use HollowsHunter.
Hollows Hunter is a command-line application with an interface similar to PE-sieve. While in case of PE-sieve you can select the process only by its PID, Hollows Hunter allows to select them by various criteria, such as:
- list of PIDs
- list of names
- the time of creation (relatively to the Hollows Hunter run time)
If no specific target is selected, it proceeds to scan all available processes.
The additional difference is, that while PE-sieve scans for hooks and patches by default, in HollowsHunter it needs to be enabled using the option /hooks.

One of the PE-sieve's use-cases is malware unpacking. Although it can be done with the primary application, MalUnpack is optimized for the best performance in this particular task.
While PE-sieve lets you scan a process that is already running, selected by its PID, MalUnpack takes as an input a path to the executable of our interest. It deploys it, and scans it repeatedly, watching for the moment when the payload got unpacked in the memory, then dumps the suspicious material. If any child processes has been created, MalUnpack follows them with the scan. After the unpacking is finished, the main process, and all the children, are automatically killed.
It is a command-line application with an interface similar to PE-sieve, exposing most of the options of the main engine, plus some new ones. Additionally, PE-sieve and MalUnpack may vary in what features are enabled by default (you can check the details by running mal_unpack with option /help).
